I have conceptualized and developed two distinctive password manager software applications, named Spring and Spring Lite, with the primary objective of empowering users to oversee their diverse usernames and passwords proficiently and securely. These software solutions have been meticulously crafted to offer a seamless user experience while consistently upholding robust security measures.
The genesis of these tools’ traces back to my arrival in the United States in February 2016, coinciding with the onset of spring. During this time, I dedicated myself to crafting these tools over the entire spring of 2016, which led to their apt nomenclature as Spring Lite and Spring. Spring Lite is a streamlined version primarily focused on managing usernames and passwords efficiently. On the other hand, Spring is a more potent and comprehensive tool, allowing seamless credential autofill for various websites. Its functionality extends to launching all my frequently used software with just a single click, significantly enhancing my daily workflow efficiency.
These applications stand as a testament to my commitment to harnessing technology to simplify and secure daily tasks. By infusing user-friendliness and robust security measures, Spring and Spring Lite aim to offer practical solutions to the challenges of password management, contributing to a more organized and secure digital existence. The core functionality of Spring and Spring Lite revolves around offering a seamless and efficient means of storing and organizing login credentials. This ensures that sensitive information remains safeguarded against unauthorized access and potential security breaches. By providing a reliable platform for password management, these applications contribute significantly to enhancing users' digital security posture.
In utilizing Spring and Spring Lite, users gain the valuable advantage of easily accessing their stored passwords whenever required. This streamlined process adds a layer of convenience to their digital interactions while maintaining a strong focus on security principles. One noteworthy aspect is the widespread adoption of these software solutions among my network of friends and close associates. This adoption speaks to the practicality and effectiveness of Spring and Spring Lite in addressing the common challenges associated with password management. This positive reception highlights the real-world impact of these applications and the trust placed in their ability to safeguard sensitive credentials.
Overall, Spring and Spring Lite are built upon a foundation of user-centric design, rigorous security measures, and practical utility. These applications stand as a testament to my dedication to creating software that not only meets practical needs but also contributes to a safer and more efficient digital landscape for users.
Secure using the Master Key:
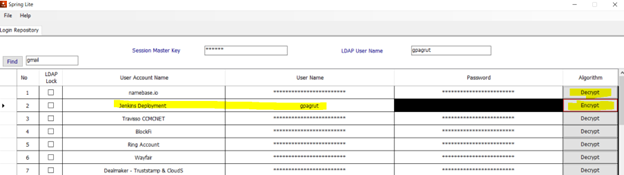
Both of these tools primarily ensure password security through the implementation of a master key system. With this approach, users have the option to safeguard all their usernames and passwords using a single master key, or they can opt to use a group of master keys to secure a smaller set of similar usernames and passwords.
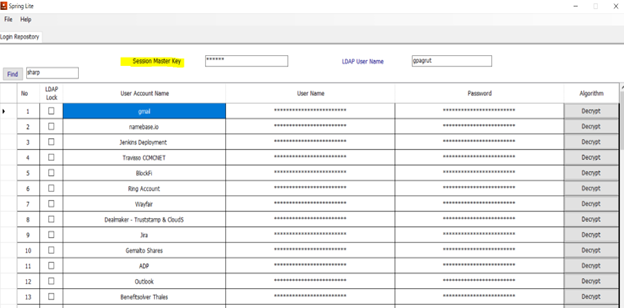
Easy to Search:
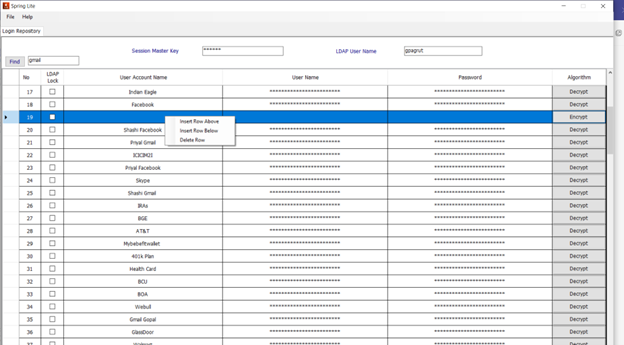
You can easily search the user account name using the find option at the top of the tool.
Tools Functions:
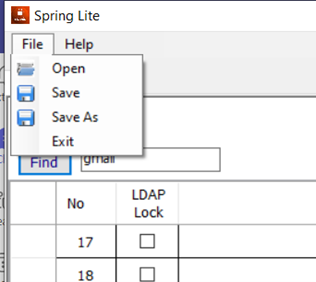
The process of accessing pre-existing encrypted passwords is straightforward and user-friendly. Users have the flexibility to save their work or opt for the "Save As" option, tailoring their actions to their specific needs. Furthermore, the application provides a seamless exit option, enhancing overall user experience and convenience.
You can easily insert any new record at any location or even you can delete the existing record.
Encryption and Decryption:
The tool employs the RSA 256 encryption algorithm to securely encrypt and decrypt its records, utilizing a single secret key for enhanced data protection. This robust encryption method ensures that the sensitive information stored within the tool remains secure and accessible only to authorized individuals with the proper decryption key. Even after encrypting the username and password, the tool further enhances security by obscuring the password with a black strip, ensuring protection against onlookers.
Advance Security:
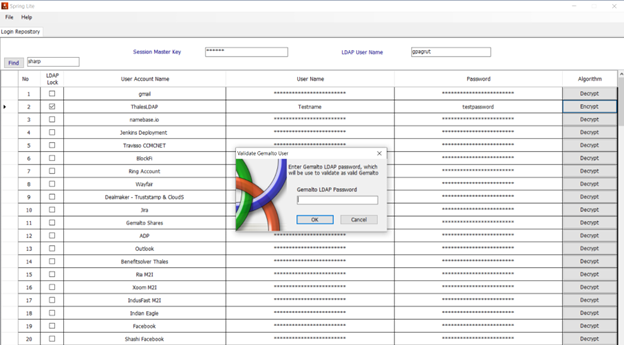
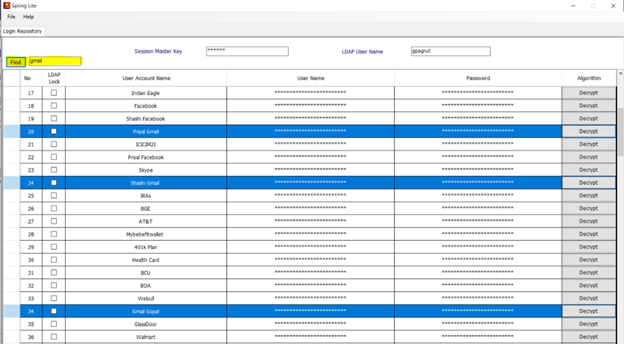
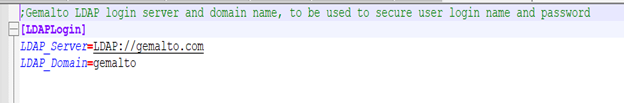
What sets this tool apart from many other password managers is its incorporation of an advanced additional layer of security. This second layer operates through the Lightweight Directory Access Protocol (LDAP), which is a vendor-neutral software protocol used to search for information or devices within a network. LDAP serves a range of purposes, from constructing a central authentication server for an organization to streamlining access to internal servers and printers. By configuring this tool with an organization's LDAP network, user validation can be conducted. This means that Spring records can be accessed solely by valid LDAP users, offering robust defense against hacking attempts through this straightforward approach.
An instance of LDAP configuration is demonstrated with the Gemalto server. It's important to note that this tool can be configured with the LDAP of any company, ensuring adaptability to various organizational setups.
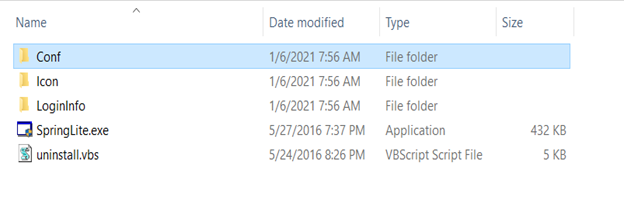
Contained within the Spring Lite installer directory are both the confirmation file and the encrypted XML file. This encrypted XML file can be conveniently carried to any location where the tool is installed, allowing you to easily access your encrypted records. This streamlined approach enables you to have all your encrypted data within a single file, making it hassle-free to use your records across various locations with a simple installation of Spring and Spring Lite.
Whenever you intend to store a username and password with the added security of the second layer, simply select the LDAP Lock checkbox, input the records, and proceed to encrypt them. When it comes time to decrypt the information, you'll need to undergo the two-step process of LDAP login and using the Master Key, ensuring a secure unveiling of your username and password record.